Applications

Six Steps to Intelligent Data Privacy
Explosive data growth is a double-edged sword. On one hand, it's enabling the most disruptive and exciting...
4 Steps to transforming employee journeys
Delivering a best-in-class employee experience is essential as remote work gains momentum. Read about...
Sauce Labs AutonomIQ SaaS App Testing Challenges
SaaS applications like Salesforce or Oracle Cloud need to be tested continuously as they undergo frequent...

A Unified Workspace delivers a transformative employee experience
A critical business edge comes from employees who are engaged, inspired and happy–thanks to the right...

Five Lessons Learned from the Pivot to a Distributed Workforce
Today, it is increasingly important to enable your employees to work remotely. Working remotely gives...

Valoir Report: Third-Party Support Goes Mainstream
Adoption of third-party support for enterprise software is now mainstream. In a report sponsored by Rimini...
Better Security. Fewer Resources.
When you consider the number of headlines that appear on a regular basis about major data breaches —...

Meet the future of work with confidence
If asked to select a word to describe the experience of the past two years, a large proportion of business...
The Challenge of Migrating Higher Education Applications to the Cloud
Explore the challenges the higher education sector faces when it comes to migrating applications to the...

Build better endpoint security to protect your entire network
The threat of a serious cyberattack is nothing new — but the situation just keeps getting more complex....

CyberArk 2022 Identity Security Threat Landscape Report
A global report from CyberArk which shows that 79% of senior security professionals say that cybersecurity...
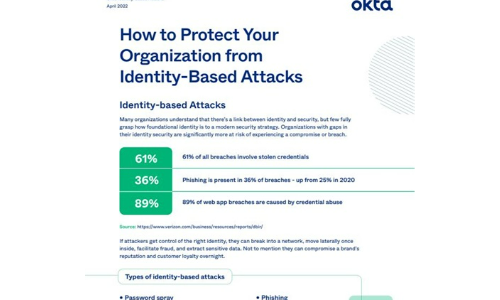
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.