Applications

Transform your business with machine learning
8 stories of machine learning success By providing the broadest and most complete set of machine learning...

VMware Cloud Foundation: Maximise Digital Business Value
76% of IT organizations are committed to hybrid cloud as a long-term strategy to quickly adapt to changing...
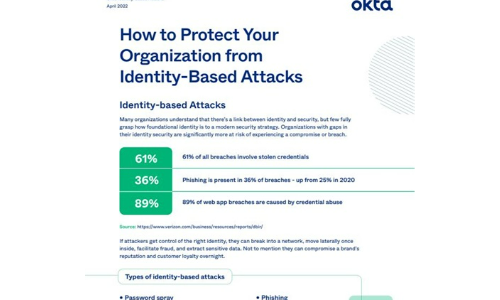
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

QandA: First Steps to a World-class Digital Workspace Experience
Most companies today measure the success of workspace initiatives using tangible cost benefits that are...

IDC: Strategies for Building Digital Infrastructure Resiliency
Multiple generations of applications. Multiple generations of infrastructure. Is there a way to reduce...

The New Workplace: Re-imagining work after 2020.
The COVID-19 pandemic has forced millions of people around the globe to stay in their homes. As a result,...

Encryption Is Now a Trojan Horse: Ignore It at Your Peril
The game of leapfrog between hackers and data security professionals continues. No sooner do organizations...

Edge Computing in Telco Networks: Gaining the Competitive Edge
Earlier this year, Wind River® teamed up with F5, Schneider Electric, and Heavy Reading on a global...

Run your Windows workloads on AWS
The best platform for Windows Server and Microsoft SQL Server Customers have been running Windows workloads...

Top 4 Pitfalls to Avoid when Deploying Office 365
There's no denying that Office 365 is a big deal. It's a big part of the Microsoft Intelligent Cloud...

Workday for The Technology Industry
Inflexible on-premise systems make it harder to keep up with the rapidly changing technology industry....

Box for banking and capital markets
One secure platform for banking and capital markets Easy, secure client experiences are the new gold...

New Era In Experience Report
We've all experienced the widespread impact of the COVID-19 pandemic. From a business perspective, the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
