Cloud
The Ultimate Guide to Document Processing Automation
Today, there are many different technologies a line of business department or automation COE are able...

Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your teams with...
The Characteristics of Your Future Technology Capabilities
Disruption -- whether big (COVID-19) or small (new start-up competitors) -- has more or less become commonplace...

Strategic Asset Management: An Infrastructure Plan for the Future
The United States faces a staggering infrastructure backlog of nearly $2.6 trillion enough to cost the...

AI-Augmented HPC From Dell Drivers Customer Successes
Science and engineering rarely stand still. Once one problem is solved, it unlocks the approach to a...

2 Steps to Achieve Endpoint Compliance with KACE® by Quest
Next to ongoing security issues, meeting compliance mandates is one of the biggest challenges IT professionals...

Telstra's Best Practice Guide to Hybrid Cloud
Hybrid Cloud is becoming the strategy of choice for enterprises that want the best of both public cloud...
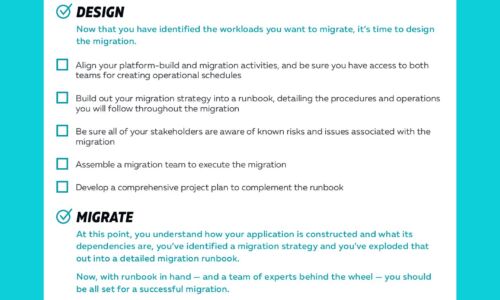
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...
How Database Performance Drives your business Success
CIOs and senior IT leaders are business enablers tasked with delivering products and services to customers...
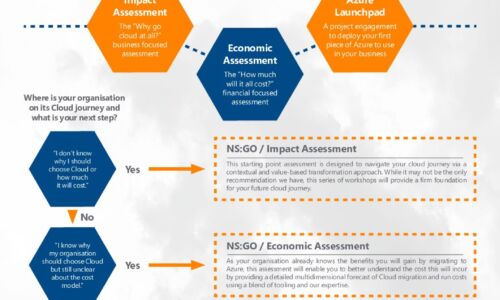
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

Complete Cloud Security for Professional Services
Thales have a long history in securing some of the world's most sensitive data, and professional service...
The UK 2020 Databerg Report Revisited Executive Summary
Cloud technology hasn't been around for long, but it's evolution in that time has been nothing less than...

Get Total Endpoint Security with KACE
As an IT professional, you're likely under pressure to manage an increasingly complex environment, while...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
