Compliance

Dynamic Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...

Four Tenets to Guide Your Enterprise's Cloud Transformation
Company leaders are increasingly turning to multi-cloud to deliver applications and other infrastructure...
Internal Firewalls for Dummies Guide
Organizations can no longer rely on edge firewalls alone to provide network security. Once attackers...

A hybrid vision for the new era of digital transformation
If you are embarking on your digital transformation journey with cloud being an integral part, the best...

Next-Gen Cloud Contact Centers RingCentral Special Edition
Finally, it's here—the new Next-Gen Cloud Contact Centers for Dummies®, RingCentral Special Edition...

Enduring from Home: COVID-19’s Impact on Business Security
Faced with shelter-in-place orders in their home counties and states, countless companies transitioned...

Three Reasons to Move from Legacy Data Loss Prevention
Changing your data loss prevention (DLP) solution is a major transition that can feel overwhelming. But...
Low-Code Guide
Low-Code development is the way to build apps more quickly by reducing the need to code. But that's not...
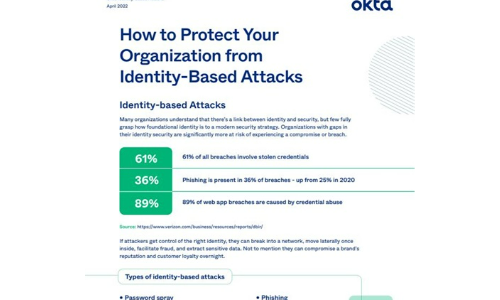
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Redefining Modern Enterprise Storage for Mission-critical Workloads
The digital business demands being placed on enterprise-scale IT organizations are now so extreme that...

Data Loss Prevention and Digital Transformation
Today's digital age has produced unprecedented amounts of data. Much of this data is considered sensitive,...

The Cloud for Better Comms
Technology has helped businesses make some giant leaps forward. But if you can't keep up with it, the...

How Effective Retailers Balance Customer Engagement and PCI Compliance
For CIOs of retail organizations, compliance with Payment Card Industry (PCI) standards is a top concern,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
