Data Center

DEVSECOPS: Staying Secured and Compliant in a High Paced Release Cycle
The rapid adoption of cloud technology and evolution of the software industry from monolithic applications...

Forrester Opportunity Snapshot: Zero Trust
Cloudflare commissioned Forrester Consulting to explore the impact of 2020's disruptions on security...

10 Reasons to Adopt E-Signature
The way we work has changed. Modern organisations are putting together new technology systems that allow...
How SD-WAN Supports Digital Transformation in Healthcare
Advancements in medicine, the increase in regulations to protect patient and doctor, and the digitization...

IDC: Blueprinting a Cloud Operating Model for the Multicloud Era
The recent acceleration of digital transformation initiatives is driving the need for a cloud operating...
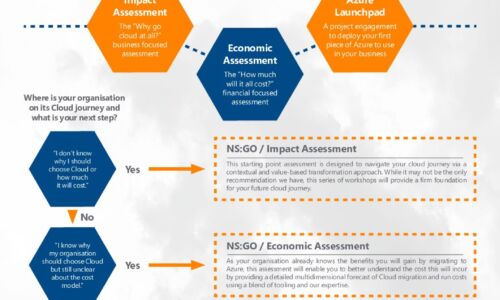
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
2021 State of Data Governance and Empowerment
Organizations are embracing their data-centric futures. They are making more data available to more people...

Making all the Right Connections
Using digital workflows to blast through barriers, drive loyalty, and accelerate growth. Organizations...
Modernize your BI Experience - Qlik Sense® and QlikView®
This datasheet provides a brief overview of the Analytics Modernization Program, which offers low-friction,...

How to Accelerate Container Adoption
Developing applications with containers has become an increasingly popular way to operationalise speed,...

Insider’s Guide To Choosing a DNS Service
The need that DNS (the domain name system) was created to address seems simple enough: where can I find...

Best Practice Makes Perfect: Malware Response in The New Normal
Before Covid-19, cyber security teams already confessed to being overworked – as high-profile security...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

