Data Center

The Keys to Digital Innovation for CIOs
Technology is now shaking up the way we work. To help IT leaders navigate the best path forward, we created...

Getting Started with Advanced Analytics
This planning guide provides valuable information and practical steps for IT managers who want to plan...

Oracle NetSuite Protects Flagship Business Applications With Illumio
Find out how SaaS leader Oracle NetSuite improves security and uptime for 7,500 application workloads...
Frost Radar™: Global SD-WAN Vendor Market,2021
Aruba earns accolades from Frost and Sullivan. Check out the Frost Radar™: Global SD-WAN Vendor Market...
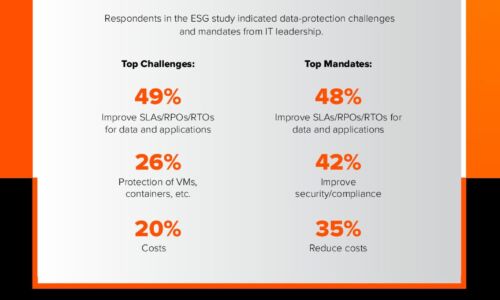
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...

Best-In-Class Email Marketing
Interactions between consumers and brands are increasingly playing out across a wide variety of different...

MGM China Strengthens Its Defenses Against Lateral Movement
World famous resort operator gains unprecedented visibility into application traffic and workload-level...
The Perfect Storm: Why MDR is Your Only Option in Modern Cybersecurity
Covid, work from home, and bring-your-own-device have expanded our threat envelopes 1000X. Attacks with...
Report: ICS/OT Cybersecurity 2021 Year in Review
Dragos is excited to present the fifth year of the annual Dragos Year In Review report on Industrial...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.