Data Center

VP AppDev Confessions
Development teams burdened with complex release requirements often run over schedule and over budget....

Ransomware Protection with Pure and Veritas
Ransomware attacks continue to be top-of-mind for business and IT leaders. And for good reason. Ransomware...
Don't pay the ransom
In simple terms, ransomware is malicious software that either encrypts your data or otherwise stops you...

Application security, fallacies + realities
The news headlines have been filled with stories about security breaches in recent months. And most of...
Learning SQL: Generate, Manipulate, and Retrieve Data
As data floods into your company, you need to put it to work right away—and SQL is the best tool for...

The Fastest Way to Modernize Apps Isn't What You Think
Future Ready with SaaS Management When it comes to digital transformation, we hold these truths to be...
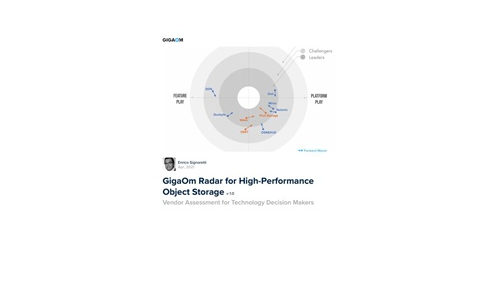
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Break down data silos
Make data available to anyone at any time. To make decisions quickly, organizations will want to store...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...

A Buyer's Guide to Audit Management Software
For today's internal audit teams, the audits themselves are only one part of a growing scope of responsibilities. Executives...

2021 State of the Threat in review
The State of the Threat report is compiled by the world-renowned Secureworks® Counter Threat Unit™...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


