
IDC white paper security
The business criticality and cyber-risk of endpoint devices could not be greater. With the COVID-19 pandemic,...
Introducing the Sotero Data Security Platform
IT security professionals continue to struggle with managing countless security solutions and disparate...
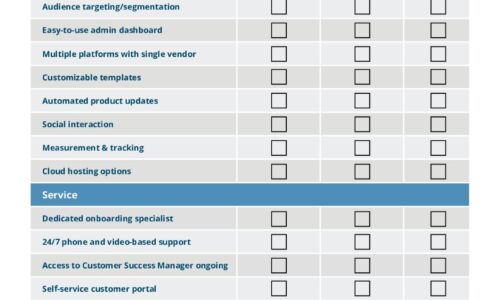
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...

Accelerating Digital Transformation through Hyper-Converged Solutions
How can organizations simplify IT in order to improve business agility, enhance financial return on investment,...
Reimagining Email Security
In the changing landscape, security and risk management leaders must ensure that existing security solutions...
Connect Everywhere: Better Voice Communications for Microsoft Teams
We used to have separate physical devices for phone calls, email and chat, and video conferencing. Over...
SASE: The Network Of The Future Is Here Today
Your business can no longer rely on the old hub-and-spoke network model with its long hauls back to the...

How Malware Can Steal Your Data
As applications drive business, more and more valuable data is accessed and exchanged through them. Cybercriminals...
3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...

The Forrester Wave™: DDoS Mitigation Solutions, Q1 2021
Cloudflare Named A 'Leader' in The Forrester Wave™: DDoS Mitigation Solutions, Q1 2021 Forrester Research,...

7 Ways to Prevent Supply Chain Phishing Attacks
Your email and digital communications with suppliers, partners, vendors and other third parties represent...

5 steps to harness the power of the organization to better serve customers
Experiences are more than just touchpoints—how customers achieve their desired outcomes is what matters. Read...

Banking on Great Conversations
The challenges of the pandemic thrust banks that were struggling to remain relevant and their customers...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
