ERP

PerimeterX is named a leader in Bot Management by Forrester
PerimeterX was named a leader in The Forrester New Wave™: Bot Management, Q1 2020. According to the...

What you need to know about upcoming ESG regulations
New ESG regulations are being proposed across the world. But ESG is about more than just meeting requirements....
A Business Case for Customer Data Management
If you're reading this, you've already arrived at a couple of realizations: This guide will help you...

How Huddle Rooms are Changing Business Collaboration
Today's successful companies know one thing for certain: they are only as good as their people. And to...

Six Steps to Successful and Efficient Threat Hunting
Rather than waiting for an alert, threat hunters proactively assume that an advanced adversary operates...
Cloud Clarity: Don't Let Complexity Derail Your Digital Strategy
Cloud has never been more important to agile, responsive organisations, but the reasons for its appeal...
Best Practices to Leverage the Cloud for Disaster Recovery
Choosing the right DRaaS solution depends on factors like supported workloads, application dependencies,...

13 Email Threat Types To Know About Right Now
Traditional email security doesn't cut it anymore. In today's rapidly evolving environment, traditional...

Adaptive Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...

5G Technology Transformation Explained
With the 5G era commencing, service providers must ensure that their infrastructures have the cloud-native,...
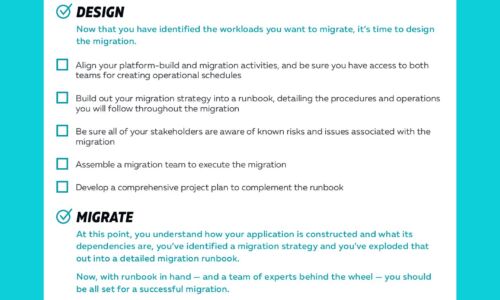
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

Flexible for the future
IT decision makers are tackling a major challenge: how can we architect our IT in a way to maximise access...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.