IT Security

7 Characteristics of Successful Hybrid Cloud Strategies
According to Gartner, by 2020, 75% of organizations will have deployed a multiload or hybrid cloud model....

A hybrid vision for the new era of digital transformation
If you are embarking on your digital transformation journey with cloud being an integral part, the best...

Security and risk management in the wake of the Log4j vulnerability
Security leaders agree: Log4j has irrevocably changed the risk landscape. Get a quick refresher on the...

Forrester Opportunity Snapshot: Zero Trust
Cloudflare commissioned Forrester Consulting to explore the impact of 2020's disruptions on security...
Driving Real Behaviour Change
Today's most potent cyber threat isn't a zero-day vulnerability, new malware or the latest exploit kit....

Definitive Guide to SOAR
How to stop threats faster with security orchestration, automation, and response. Cybersecurity organizations...
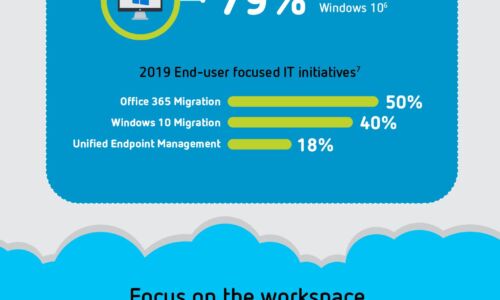
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Take the fight to the cybercriminals
An IT leader's guide to keeping your business running with proactive cybersecurity. It's an incredibly...

Digital acceleration in the time of coronavirus
Business decision-makers around the world were collectively blindsided by the scale and speed that working...

Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...

The Business Email Compromise Handbook
A Six-Step Plan for Stopping Payment Redirection, Supplier Invoicing Fraud and Gift Card Scams Sometimes,...

Advanced MySQL 8
Design cost-efficient database solutions, scale enterprise operations and reduce overhead business costs...

Penetration Testing For Dummies
Target, test, analyze, and report on security vulnerabilities with pen-testing Pen-Testing is necessary...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
