Malware

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...

The New Reality: Bring Order To Chaos With Unified Endpoint Security
Chaos and confusion dominated the enterprise cybersecurity landscape even before the COVID-19 pandemic...
Deploying Flexible Data Protection to Support Cloud Workload Placement
Digital transformation (DX) projects are designed to help organizations better utilize data for competitive...

Why a Backup Strategy for Office 365 is Essential
This short, easy-to-read research paper by IDC provides their view on why having a backup of Office 365...
Cybersecurity: A Short Business Guide
The news often reports on incidents involving large corporations facing massive data breaches where the...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...

Increase the ROI of Inspection Technologies with F5 Orchestrator
Recent analysis by F5 Labs shows that 68% of malware installed through phishing is hiding in encryption....
The Hidden Cost of Free M365 Security Features
All email, cloud, and compliance solutions are not created equal. As organisations make the move to Microsoft...

Cybersecurity For Dummies
Advanced threats have changed the world of enterprise security and how organizations are attacked. These...
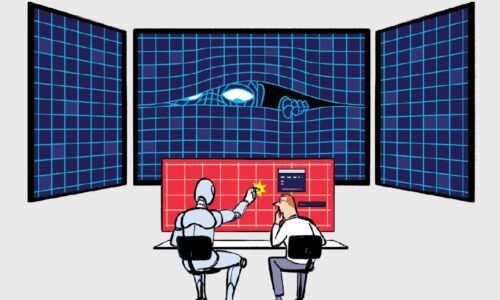
Transforming the SOC: Building Tomorrow’s Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Lacework 2021 Cloud Threat Report, Volume 1
The Lacework Labs team provides quarterly reports focused on risks and threats relevant to cloud services,...
A Guide To Implementing a Secure SAP System with Fortinet
With today's rapidly changing market conditions and economic climate, organizations are using enterprise...

BIOS Security – The Next Frontier for Endpoint Protection
Everyone is familiar with the process of booting up a computer. Many of us do this every day — pressing...
The Perfect Storm: Why MDR is Your Only Option in Modern Cybersecurity
Covid, work from home, and bring-your-own-device have expanded our threat envelopes 1000X. Attacks with...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.