Network

How to Ensure Flexibility in a HMC Strategy
Enterprises are moving rapidly to diverse cloud models, including hybrid cloud, multicloud and connected...

Advanced Email Security
Email is a fundamental feature of modern business. Yet it is also the number one threat vector. Email...

CISO Guide: Securing Cloud Communication and Collaboration
With UCaaS platforms accelerating innovation and sharing in productivity resources like chat, voice,...

Best-In-Class Email Marketing
Interactions between consumers and brands are increasingly playing out across a wide variety of different...

Secure Access To Over 150 Systems, For Over 2000 Diverse Users
A global leader in the field of smart energy was looking to provide better and secure remote access to...

Migrate, modernize, transform
To win in the digital era, companies are seeking new ways to build apps and services, connect previously...
We've saved time, money and resource
Come and see how we upgraded our ServiceNow production instance to Paris in 28 hours and learn how Motorola...

The Road to Recovery - Growing Your Business in China
The pandemic is fast tracking the digital transformation of organisations in China (and the region) as...
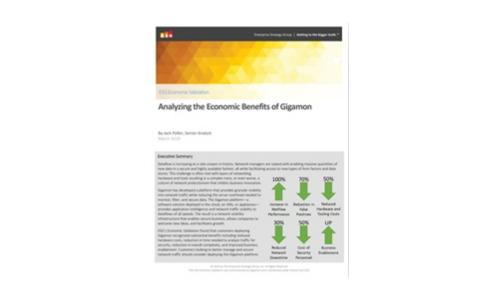
Analyzing the Economic Benefits of Gigamon
This ESG Economic Validation is focused on the changes companies can expect when deploying Gigamon's...

Citrix SD-WAN for Azure Virtual WAN
A partnership that puts you first. Citrix is a Microsoft Virtual WAN preferred partner. This means that...

Running Windows on AWS eBook
Migration to the cloud is not merely a journey, it's a major step toward business transformation—and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.