Network

Creative Trends 2022
The seriousness of life during the pandemic has taken its toll. Tired of the mundane and familiar, people...
Deliver agility with an expanded vision for S&OP
Though sales and operations planning (S&OP) originally aspired to bring business functions together for...

GigaOm Radar for Phishing Prevention & Detection
Get your complimentary copy of this independent GigaOm Research report, which analyzes positioning and...
Identity is Key to Stopping These 5 Cyber Security Attacks
A secure enterprise is a successful enterprise. Security threats are a massive burden for most organizations—but...

Oracle Cloud@Customer Brings Full Cloud Experience On-Premises
Oracle Autonomous Database on Exadata Cloud@Customer and Dedicated Region Cloud@Customer powered by 2nd...
The Need for Speed: Second Generation EDR
Endpoint security plays an integral role in modern security architecture. While initially focused on...
Investa Adds Micro-Segmentation to Security Portfolio
As one of Australia's largest commercial real estate companies, Investa has a powerhouse portfolio worth...
The Role of Machine Learning and Automation in Storage
There has been lots of hype around the increasing role that machine learning, and artificial intelligence...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...
Alphabet Soup: Making Sense of XDR, EDR, NDR, and SIEM
XDR, EDR, NDR, and SIEM. They are among the most prominent acronyms in cybersecurity. But what do they...
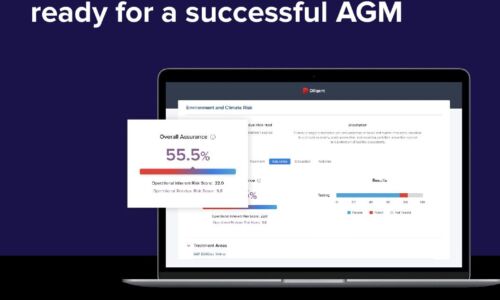
4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....

Four Data & Analytics Trends to Watch in 2020
The buzz around headline-grabbing topics like machine learning (ML) and artificial intelligence (AI)...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.