SaaS
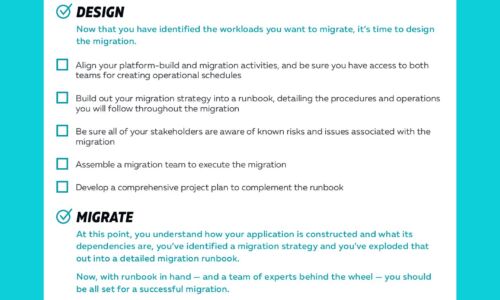
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

What is usage data and how do businesses use it?
What exactly is usage data? How does it relate to subscriptions and billing? Why is processing usage...

Facing the future: Digitization in the Public Sector
The continuous improvement with the capabilities of business technologies – like cloud computing and...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...
Aberdeen Customer Operations
This report by Aberdeen reveals the role and impact of customer operations on service and back-office...

File Services with Azure NetApp Files and Cloud Volumes Service
NetApp Cloud Volumes Service and Azure NetApp Files offer something brand new: a fully-managed service...

6 Ways to Deliver Business Value from your Cloud Data Warehouse
Data-driven digital transformation requires the ability to deliver trustworthy insights faster than your...
Reporting Made Easy: 3 Steps to a Stronger KPI Strategy
Are you drowning in meaningless metrics? Creating smarter reports and tracking KPIs is a must, but it...

Forrester: Hyperautomation leads to transformative business outcomes
This Forrester Consulting Opportunity Snapshot looks at Hyperautomation, and how it is central to business...
Sotero Data-In-Use Encryption
Though encryption is the most effective way to reduce the probability of a security breach, traditional...

Definitive Guide to Internet Isolation
The traditional approach to cybersecurity has reached its potential, and attackers have learned how to...

CISO's Playbook to Cloud Security
To secure enterprise assets in the cloud, CISO's must address several new challenges unseen in traditional...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

