Server

5 Critical Requirements for Internal Firewalling in the Data Center
Preventing hackers from hiding inside large volumes of east-west network traffic has now become critical...

Introduction to AWS Security
Raise your security posture with AWS infrastructure and services. AWS's approach to security, including...

Security Starts Here: Privileged Access Management
The threat of a security incident or critical error is very real, and it's something that auditors are...

Choosing the Right RAID—Which RAID Level is Right for You?
For any organization, whether it be small business or a data center, lost data means lost business. There...

Cybersecurity for the Modern Era
The book explores how cyber attacks and compliance issues are evolving and outlines how you can create...
How SD-WAN Supports Digital Transformation in Healthcare
Advancements in medicine, the increase in regulations to protect patient and doctor, and the digitization...
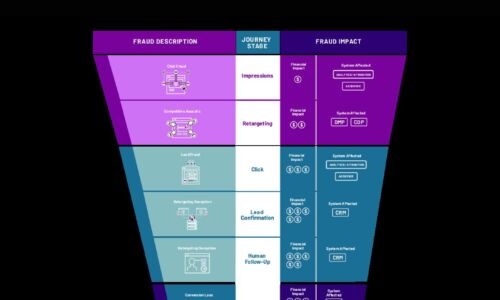
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Functional Programming For Dummies
Using functional programming techniques can make you incredibly efficient when solving certain problems...

6 ways cloud computing can support your security capabilities
Embracing cloud computing forces organizations to decide between the cost-effectiveness, scalability,...

The Future Is Flexible: Six Areas to Make It Work.
Over 50% of businesses are preparing for long-term, flexible work patterns. But the rush to adopt remote...

BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...

The Business Value of Red Hat Runtimes
IDC has addressed organizations that have deployed Red Hat® Runtime's solutions as a foundation for...
Multi-Factor Authentication Buyer's Guide
With the increase in phishing and data breaches over the last few years, the chances are that your login...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
