Service Providers
Inherent Vulnerabilities Harming Telecommunications Companies
Telecommunications companies are among the most targeted companies in the world, attracting the most...

12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...

How SASE empowers your business for the cloud generation.
Wide area networks (WANs) have played a critical role in business growth for several decades. Early WANs...

Finding a Setting Worthy of Your “Crown Jewels”
Keep all the Data in a single, unified Database – Oracle Exadata For most companies, data is critical...

Securing financial services network data
Financial services is one of the most tightly regulated business sectors. The FSA, the Data Protection...

CompTIA A+ Certification All-in-One For Dummies, 5th Edition
Fully updated to cover the 2019 exam release! CompTIA's A+ certification is an essential certification...
Achieving Data Excellence in Financial Information Management
Financial institutions have accumulated large quantities of valuable data and metadata, but the levels...
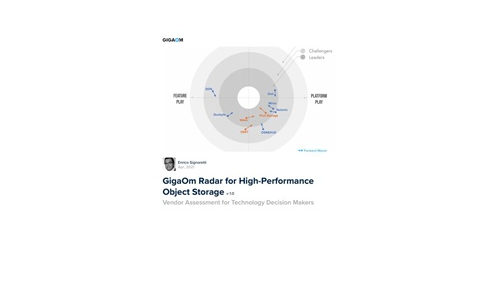
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Evolving From Operating IT To Orchestrating IT
Organisations realise the time is now to move to a new deployment model. Digital transformation and proliferation...

Edge Computing in Telco Networks: Gaining the Competitive Edge
Earlier this year, Wind River® teamed up with F5, Schneider Electric, and Heavy Reading on a global...
Delivering Secure Financial Services for Your Customers in the Cloud
How financial firms build stellar experiences in the cloud From ordering takeout on an app to joining...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.