Virtualization
How Intrinsic Security Protects Against Business Disruption
When it comes to IT, disruption is just another day at the office. From fending off cyberattacks to incorporating...

Building a Winning Data Strategy
The potential of data to drive business value and create opportunities is well recognized by organizations...
SASE & ZTNA for Dummies
SASE and ZTNA combine SD-WAN efficiencies with a flexible, user-centric approach to securing remote workers...
The evolution of process automation
Automation has a long and storied history. Today, advancements in artificial intelligence (AI) are spawning...

Deliver more reliable digital services by knowing what supports them
When a critical IT service goes down in your enterprise, how can you quickly determine the root cause,...

5 ways Citrix Workspace puts user experience first
As technology has become integrated into almost every facet of how we work and live, user experience...

Respond and Evolve with Your Multi-Cloud
In a world of uncertainty, organizations on traditional IT platforms need something they can rely on...
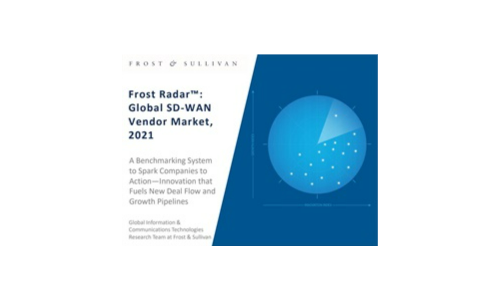
Frost Radar™: Global SD-WAN Vendor Market,2021
Aruba earns accolades from Frost and Sullivan. Check out the Frost Radar™: Global SD-WAN Vendor Market...
High-performance persistent storage for virtualized workloads
Supporting virtualized workloads in Red Hat® OpenShift® requires reliable persistent storage that offers...

Modern upgrade opportunities powered by Veeam DataLabs
With the upcoming end of life of Microsoft Windows server 2008 R2, organizations need to have a plan...

Database Solutions Pocket Book
Given the fast pace of modern business, traditional enterprise infrastructure is ill-suited to meet the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

