Latest Whitepapers

Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...

Unified Fast File and Object (UFFO) Storage
In this book, you get an idea of the vast potential for unstructured data — and also the infrastructure...

How To Stop Lateral Attacks With Workload Microsegmentation
Network segmentation is a widely accepted tool for improving performance and boosting security. By splitting...
The Road To Digital Experience Success
The world of work is not changing. It has already changed. Firms that have not boarded the ship need...

CMO's Guide to AI for Customer-Centric Marketing
AI allows marketing leaders and their teams to quickly analyze vast amounts of customer data to predict...

Quest® KACE® SMA reduces software license compliance stress
Do you know whether all your software licenses are compliant? Your IT landscape has gotten more and more...
How to Integrate DocuSign
A smooth integration is key to the success of any digital transformation project. Many organisations...

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...

Drive Infrastructure Optimization with Predictive Analytics
As cloud architects move more workloads to public and private clouds, hybrid multicloud architectures...

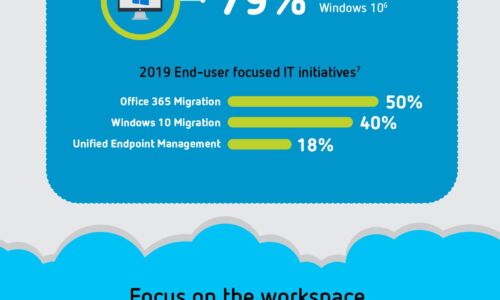
Organizations Accelerating Their Digital Workplace Achieve Improvements
This study sought to understand whether, and to what degree, an organization's adoption of modern device...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.