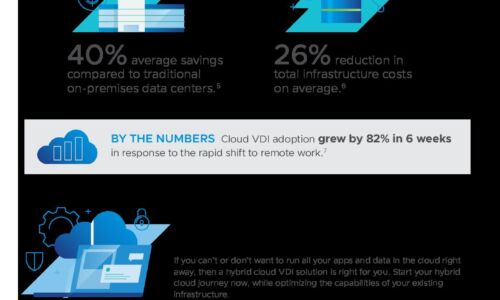
Cloud Computing

Securing Cloud Transformation with a Zero Trust Approach
When it comes to rates of change, cybersecurity has rightly been on the conservative side. Setting up...

The Fastest Way to Modernize Apps Isn't What You Think
Future Ready with SaaS Management When it comes to digital transformation, we hold these truths to be...
Defend Against Ransomware
Defend your organization from evolving ransomware attacks. Learn what it takes to reduce risk and strengthen...
13 Questions You Must Ask Your Bot Mitigation Vendor
Today, bots are a hot topic, one that affects all web applications. As a result, many vendors are trying...
How To Choose a Managed Extended Detection and Response Solution
Organizations face major cybersecurity hurdles. The first challenge is finding effective cybersecurity...
Aruba's Roadmap To Hybrid Workplace Success
After the initial network overhaul to enable work from home at the start of the pandemic, organizations...

Encryption, Privacy, and Data Protection: A Balancing Act
The Business, Privacy, and Security Mandates for Comprehensive SSL/TLS Inspection. Enterprise IT leaders...

CompTIA A+ Certification All-in-One For Dummies, 5th Edition
Fully updated to cover the 2019 exam release! CompTIA's A+ certification is an essential certification...

5 signs your SaaS company needs to improve its usage data management
If your SaaS company offers usage-based pricing, there's a good chance you've built an in-house solution...

Speed Up Process Change for SAP ERP
The ability to move fast and having a rapid response to change is needed for businesses to innovate faster....
Fortinet Federal Government Cybersecurity Solutions
U.S. federal agencies operate some of the world's largest and most complex digital networks, but many...

Top Ten Tips When Buying A Raid Adapter
RAID (Redundant Array of Inexpensive Disks) is a data storage structure that allows a system administrator...
Report: Forrester TEI for CSM
To deliver effortless, end-to-end customer experience every time, all parts of your organisation need...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.