Cloud Computing
State of Ransomware: Invest now or pay later
Ransomware attacks continue at a blistering pace because organizations remain vulnerable to the exploits...

Accelerate Your Multi-Cloud Transformation
While the business goals and schedule for this cloud-first approach are often well-defined, the path...

Why aren’t factories as smart as they could be?
Data is revolutionizing manufacturing. Combined with powerful tools like artificial intelligence/machine...

Box for Banking
Simplify banking for your customers in the cloud I got into banking to push paper and fill out forms....

Protect your organization from ransomware
Get a glimpse of the criminal players who operate within the underground ransomware economy. We'll help...

Oracle Autonomous Database for Dummies
What if your database could install, manage, secure, and upgrade itself—with little or no manual administration...

5 Myths about Privileged Access Security for AWS
In today's modern enterprise, more companies rely on an IaaS model. In fact, 93% of IT decision makers...
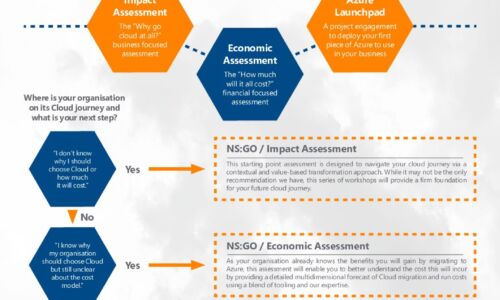
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
4 steps to transforming employee journeys
Delivering a best-in-class employee experience is essential as remote work gains momentum. Read about...
How chemical companies can achieve a new level of enterprise performance
Mastering the challenges of an ever-evolving enterprise has always been a fundamental part of the day-to-day...

Sharing the Workload of Workload Security
Security teams need the help of IT operations to secure workloads IT admins and security teams both play...

Achieving Zero Trust Segmentation With Illumio
This comprehensive guide explains the critical need for Zero Trust Segmentation and how Illumio can help...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.