SAN
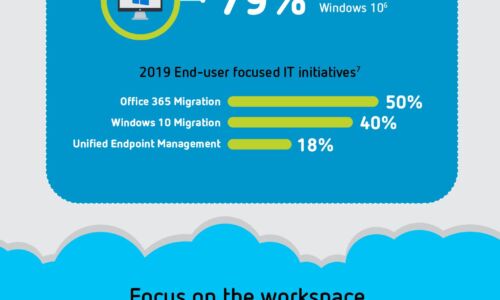
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Osterman Research: How to Comply with the CPRA Report
With the unprecedented ability of organizations to digitally collect, process and sell personal data...

Office of the CTO Report: Continuous API Sprawl
APIs are a contract between the service provider and service consumer. When any application uses an API,...

The CIO’s guide to aligning technology and business strategy
Hyperautomation and low code edition Inside this CIO Guide, you'll find solutions to the problems that...
CISO strategies for proactive threat prevention
Security leaders are under immense pressure to protect their organizations from cyberattacks. But the...

Proofpoint Security Awareness Training
Proofpoint Security Awareness Training Enterprise helps you deliver the right training to the right people...
How to chose a managed extended detection and response solution
Managed Detection and Response (MDR) solutions are specialized security services that allow an organization...

The Forrester Wave™: Enterprise Email Security, Q2 2021
In a 25-criterion evaluation of enterprise email security providers, Forrester identified the 15 most...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.