SAN
Safeguard Your Infrastructure from Ransomware and Cyber Threats
Data, the new currency of the global economy, has become the single most valuable asset for a majority...

7 Key Considerations for Microservices-Based Application Delivery
As you modernize your applications with microservices-based architecture and Kubernetes, you must also...

Addressing Multiple Concerns with a Single Solution
Organizations have been steadily implementing digital innovations for years, but recently the pace of...
2021 Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your DevSecOps...
Detect and Stop Advanced Threats Faster to Reduce Security Risk
As cyber adversaries become more sophisticated, organizations are forced to constantly upgrade their...

Next-Gen iPaaS For Dummies
Digital Transformation changes expectations: better service, faster delivery, with less cost. Businesses...

State Of Software Security Executive Summary
This quick summary from the detailed State of Software Security Report provides insights into the most...

CMO’s Guide to AI for Customer-Centric Marketing
AI allows marketing leaders and their teams to quickly analyze vast amounts of customer data to predict...
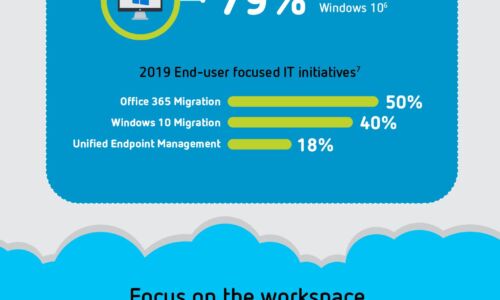
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...
How To Choose a Managed Extended Detection and Response Solution
Organizations face major cybersecurity hurdles. The first challenge is finding effective cybersecurity...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



