Telecommunications
EMA Report: Availability and Buying Options in the Emerging SASE Market
Cloudflare One reviewed as a leading provider of Secure Access Service Edge Gartner's Secure Access Service...
UCaaS: Cloud Calling
Cloud Calling provides a secure and resilient platform of feature rich voice communications with true...

Finding a Setting Worthy of Your 'Crown Jewels'
Keep all the Data in a single, unified Database – Oracle Exadata For most companies, data is critical...

2021 State of the Phish
There's no question that organisations (and individuals) faced many challenges in 2020, both new and...

Make Artificial Intelligence Real
There's nothing artificial about making the world a better place. Over the last several decades, technology...

Cybersecurity for the Modern Era
The book explores how cyber attacks and compliance issues are evolving and outlines how you can create...
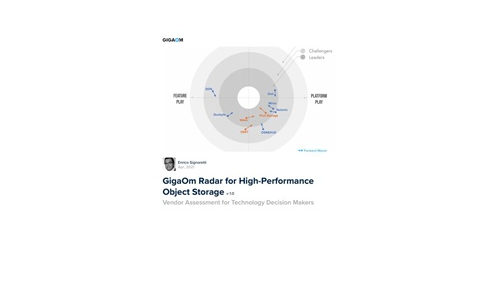
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Chatbot Starter’s Guide
Is your contact center struggling to determine which chatbot solution is right for you? This eBook can...
Cloud Clarity: Don't Let Complexity Derail Your Digital Strategy
Cloud has never been more important to agile, responsive organisations, but the reasons for its appeal...

5G Technology Transformation Explained
With the 5G era commencing, service providers must ensure that their infrastructures have the cloud-native,...

NETSCOUT Threat Intelligence Report 1H 2020
COVID-19 has driven both workforces and consumers online – but the lockdown also saw DDoS attack frequency...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.