Software

Upgrade to State-of-the-Art Log Management
Most log messages traditionally come from three types: system logs of servers, network devices, and applications....

The Definitive Guide to SharePoint Migration Planning
Getting your SharePoint migration right is essential to a host of important goals, from business continuity...

4 Best Examples of Field Service Management
Software Built for the Future. Field service management software is quickly becoming a must-have for...

Case Study - The Student Hotel
The Student Hotel wants to rethink the hospitality sector. It aims to create flexible, multi dimensional...
Common Browser Isolation challenges, and how to overcome them
A growing number of security teams are implementing a Zero Trust security strategy, in which no application,...
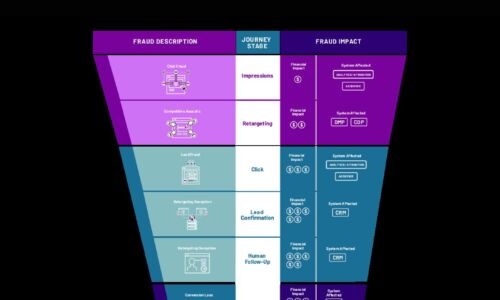
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

7 Reasons VMware Cloud Foundation is the Premier Hybrid Cloud Solution
Is your IT service delivery future ready? Application and cloud strategies are inextricably linked, and...

Marketing and IT: The Digital Transformation Dream Team
Brands need to take more control over how they engage customers. To make this happen, Marketing and IT...
Achieving success with your S/4HANA proof of concept (POC)
The value of S/4HANA is now well accepted. During a recent survey, an overwhelming majority of the 480...

11 Recommended Security Practices to Manage the Container Lifecycle
This paper details 11 recommended practices for DevSecOps teams needing to move to a more modern application...

Moving to a Cloud Data Warehouse on Amazon Redshift
The challenge for today's enterprises is to extract the most value from their data. To do so, companies...
Investa Adds Micro-Segmentation to Security Portfolio
As one of Australia's largest commercial real estate companies, Investa has a powerhouse portfolio worth...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

