Software

Multi-Cloud IT Executive Buyer's Guide
Intentionally establishing a multi-cloud strategy is a powerful way to modernize your IT infrastructure...
Report: Forrester TEI for CSM
To deliver effortless, end-to-end customer experience every time, all parts of your organisation need...

C-Level Guide to Accelerating Software Delivery Through Automation
Digital transformation is near the top of every CIO's agenda today. To reap the benefits, it's critical...

Deliver more reliable digital services by knowing what supports them
When a critical IT service goes down in your enterprise, how can you quickly determine the root cause,...

The Collaboration Checklist: 8 Questions Every IT Leader Should Ask
Collaboration software can do much more than simple messaging or conferencing. Choose the right platform...

4 Low-Code Best Practices for SAP Fiori Apps
It has been proven that enterprise IT teams that include a no-code/low-code approach for their SAP app...

The Road to Recovery - Growing Your Business in China
The pandemic is fast tracking the digital transformation of organisations in China (and the region) as...
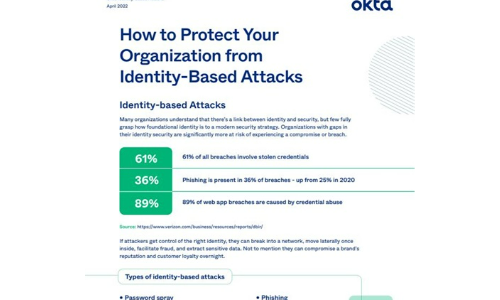
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

For digital sovereignty and transparency in the cloud
Shared use of infrastructure not only saves resources but also enables companies to push ahead with digitalisation...
Vulnerability and Patch Management
Patching vulnerabilities is a constant battle for organizations, which is why threat actors frequently...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.