Software

5 stages of security automation maturity: how do you compare?
Security automation has the power to help enable enterprise transformation through improving operational...

Would you be ready.... if dads get a 2.5 year paternity leave?
Midsize companies play a key role in the global economy, driving a large share of job creation, economic...
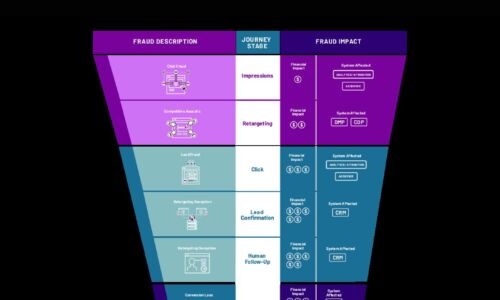
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Accelerating Your AWS Journey
Migrate and modernize to accelerate operational efficiency. Get the speed and agility you need to delight...

Build your future, faster
To support the organization in its pursuit of innovation, and to address future uncertainties, development...
Connect Everywhere: Better Voice Communications for Microsoft Teams
We used to have separate physical devices for phone calls, email and chat, and video conferencing. Over...
Forrester : Managing Security Risk and Compliance
The explosion of data and proliferation of devices demands better security tools and monitoring from...

Three Steps to a Stronger Healthcare Organization
Healthcare workers are on the front lines of these challenges, delivering care, keeping the organization...

Machine learning drives impact
While machine learning (ML) has moved beyond the hype to become a meaningful driver of value, many organizations...
Data as a Strategic Growth Asset in 2021
In Q1 of 2021, WBR Insights surveyed 100 Chief Data Officers and similar from buy-side and sell-side...
HP Proactive Insights Experience Management
Today's work environment looks a lot different than it used to. And it's still evolving. More of us are...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.